The World of Virtual Wallets
How People Use Technology as Their Digital Currency
In modern times, almost everyone carries a cell phone with them. Many companies, businesses, and organizations have taken advantage of this growing trend to make the ease to which they appeal to their customers even easier through the utilization of technology. From generating apps to sending mass emails, companies are becoming more tech-savvy with how they are appealing to the general public in order to generate sales.
One major component of this is through the recently developing use of digital currency. Through applications and programs such as Apple Pay, Venmo and Zelle, people are able to send transactions from the tap of their phone or smart watch. There’s no more trips to the bank, writing checks, finding the nearest ATM machine or mailing your latest bill payments.
While digital and cryptocurrencies such as Bitcoin are rapidly growing, some are hesitant to invest the over $4,000USD to receive only 1 bitcoin in return. Another concern is that the currency that it is converted into is one that is not tangible or redeemable in any location except through digital means.
As an in-between, many have turned to apps such as Venmo or Zelle that link to one’s credit card, debit card or bank account in order to easily transfer funds to friends, family, and others who they may need to repay. App users are also given the feature to request funds from other individuals who may owe a given amount of money.
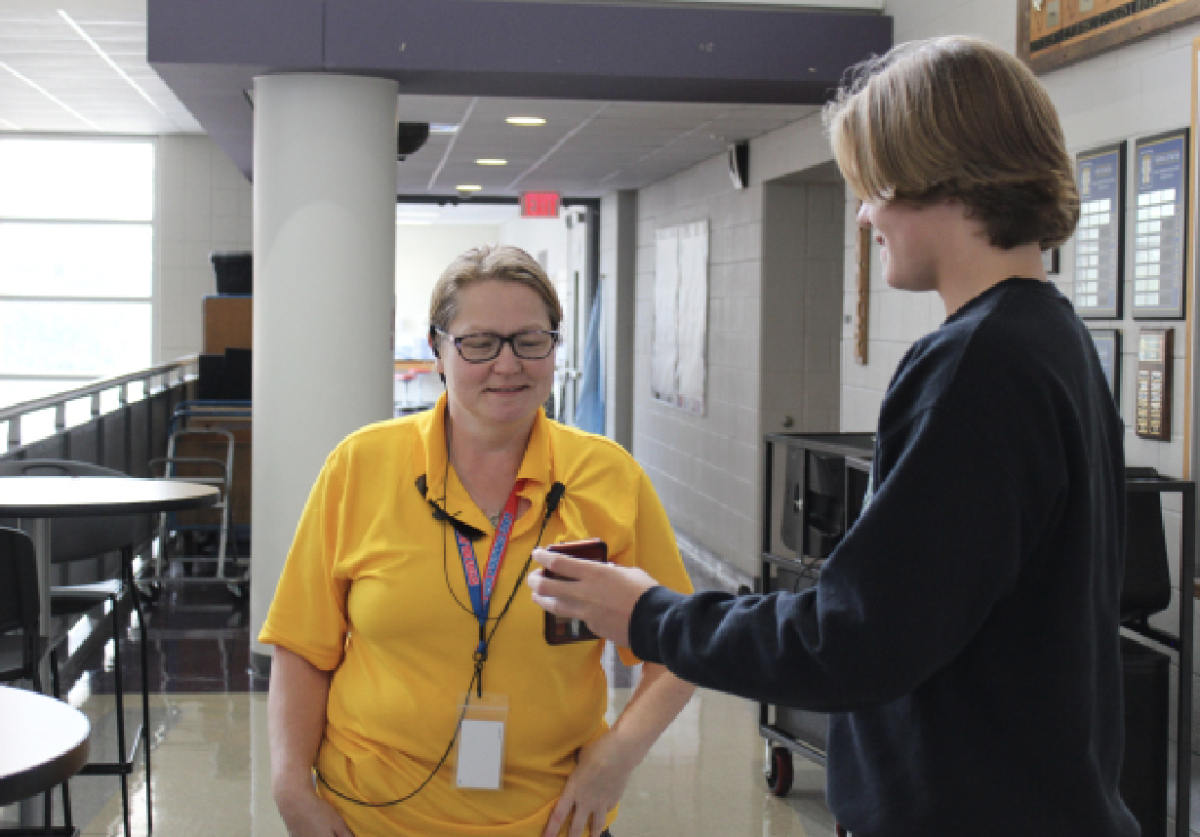
Apps like these are often common around younger demographics – especially those who have grown up with technology and are accustomed to how it works. Others are rather skeptical of these apps, as they worry that the programs pose potential privacy and security threats to users.
While this a valid and arguable claim, nearly all the developers of these applications have worked to create a system in which the data of its users is protected in a way that is encrypted with complex security features such as two factor authentication and multiple passwords.
As programs like these continue to surface, it will be interesting to see how it will continue developing in the quickly-changing worlds of technology and economics.